This will be a very quick post. While reading about code security, I came through a concept called “Security through obscurity” and when I dig in, I realized code obfuscation is great way to do it. But then, I thought how Orchestrator handles obfuscated code. And so I tried and let me give you a quick demo on that.
What is Code Obfuscation?
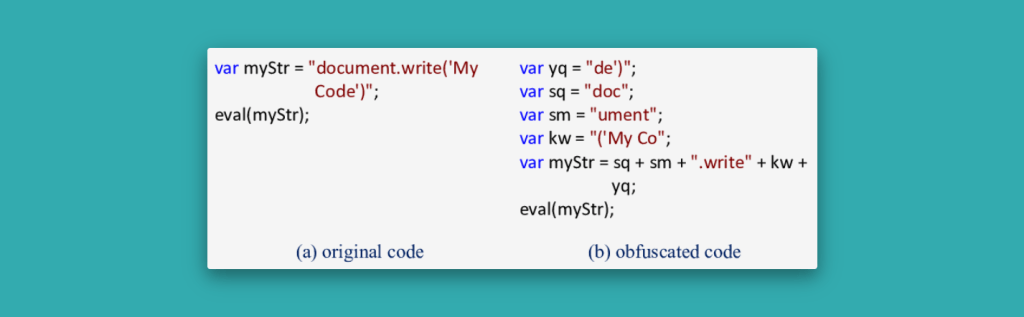
Before going to Orchestrator, let’s briefly understand what exactly code obfuscation is. Obfuscation is the act of creating code that is difficult for humans to understand. It may use needlessly roundabout expressions to compose statements. Programmers may deliberately obfuscate code to conceal its purpose or its logic or implicit values embedded in it, primarily, in order to prevent tampering, or even to create a challenge for someone reading the source code.
Demo
An Example JavaScript Code
Let’s take an example script. Here, we have a vRO action which decodes vSphere license details using vRO Scripting APIs.
/**
* @version 0.0.0
* @description Decodes the 'Product Name' and 'Product Version' from a vSphere license string
*
* @param {VC:SdkConnection} vCenterConnection
* @param {string} licenseKey
*
* @outputType string
*
*/
//validate that we have a license key that is 5, 5 character strings delimited by a '-'
var licenseParts = licenseKey.split('-');
if (licenseParts.length != 5) {
throw("license key is not complete");
}
for (var part in licenseParts) {
if (licenseParts[part].length < 5) {
throw("license key is invalid. Section: '"+licenseParts[part]+"' of '"+licenseKey+"' is too short");
}
if (licenseParts[part].length > 5) {
throw("license key is invalid. Section: '"+licenseParts[part]+"' of '"+licenseKey+"' is too long");
}
}
var licenseInfo = vCenterConnection.licenseManager.decodeLicense(licenseKey);
System.log("License Name: "+licenseInfo.name);
var licenseProps = licenseInfo.properties;
for (var lp in licenseProps) {
if (licenseProps[lp].key === "ProductName") {
System.log("Product Name: "+licenseProps[lp].value);
} else if (licenseProps[lp].key === "ProductVersion") {
System.log("Product Version: "+licenseProps[lp].value);
}
}
/* Example Output
License Name: vSphere 7 Enterprise Plus
Product Name: VMware ESX Server
Product Version: 7.0
*/It takes 2 inputs. Select vCenter and provide a licenseKey in this format XXXXQ-YYTYA-ZZ1G8-0N8K2-05D6J)

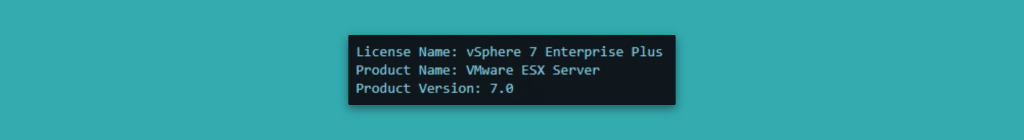
Let’s run it. The output will be similar to
Convert code using Obfuscator Tool
To obfuscate my JavaScript code, I used this tool available at https://obfuscator.io/
After conversion, I copied the code.
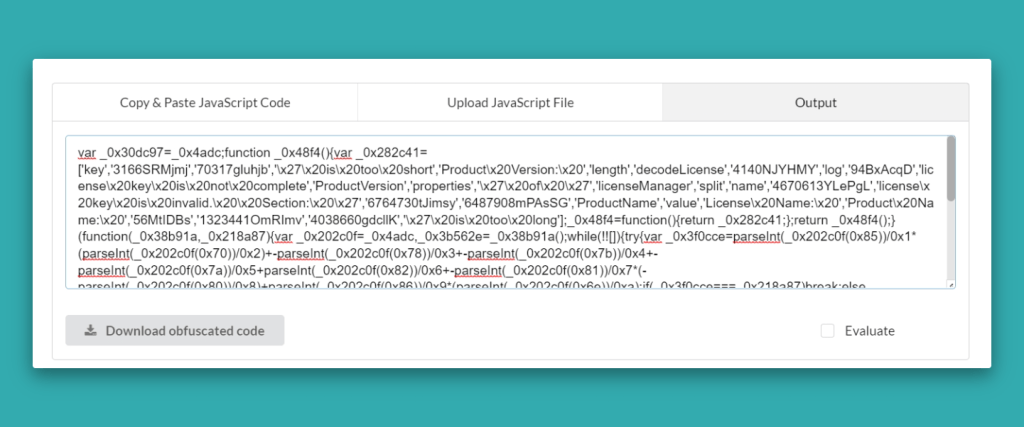
And it look like this
var _0x30dc97=_0x4adc;function _0x48f4(){var _0x282c41=['key','3166SRMjmj','70317gluhjb','\x27\x20is\x20too\x20short','Product\x20Version:\x20','length','decodeLicense','4140NJYHMY','log','94BxAcqD','license\x20key\x20is\x20not\x20complete','ProductVersion','properties','\x27\x20of\x20\x27','licenseManager','split','name','4670613YLePgL','license\x20key\x20is\x20invalid.\x20\x20Section:\x20\x27','6764730tJimsy','6487908mPAsSG','ProductName','value','License\x20Name:\x20','Product\x20Name:\x20','56MtIDBs','1323441OmRImv','4038660gdcllK','\x27\x20is\x20too\x20long'];_0x48f4=function(){return _0x282c41;};return _0x48f4();}(function(_0x38b91a,_0x218a87){var _0x202c0f=_0x4adc,_0x3b562e=_0x38b91a();while(!![]){try{var _0x3f0cce=parseInt(_0x202c0f(0x85))/0x1*(parseInt(_0x202c0f(0x70))/0x2)+-parseInt(_0x202c0f(0x78))/0x3+-parseInt(_0x202c0f(0x7b))/0x4+-parseInt(_0x202c0f(0x7a))/0x5+parseInt(_0x202c0f(0x82))/0x6+-parseInt(_0x202c0f(0x81))/0x7*(-parseInt(_0x202c0f(0x80))/0x8)+parseInt(_0x202c0f(0x86))/0x9*(parseInt(_0x202c0f(0x6e))/0xa);if(_0x3f0cce===_0x218a87)break;else _0x3b562e['push'](_0x3b562e['shift']());}catch(_0x2ca51c){_0x3b562e['push'](_0x3b562e['shift']());}}}(_0x48f4,0xcf10d));var licenseParts=licenseKey[_0x30dc97(0x76)]('-');if(licenseParts['length']!=0x5)throw _0x30dc97(0x71);for(var part in licenseParts){if(licenseParts[part]['length']<0x5)throw _0x30dc97(0x79)+licenseParts[part]+_0x30dc97(0x74)+licenseKey+_0x30dc97(0x87);if(licenseParts[part][_0x30dc97(0x89)]>0x5)throw _0x30dc97(0x79)+licenseParts[part]+_0x30dc97(0x74)+licenseKey+_0x30dc97(0x83);}var licenseInfo=vCenterConnection[_0x30dc97(0x75)][_0x30dc97(0x8a)](licenseKey);System[_0x30dc97(0x6f)](_0x30dc97(0x7e)+licenseInfo[_0x30dc97(0x77)]);function _0x4adc(_0x4d2f0a,_0x40aefd){var _0x48f4ef=_0x48f4();return _0x4adc=function(_0x4adcaf,_0x1f587e){_0x4adcaf=_0x4adcaf-0x6e;var _0x2861fc=_0x48f4ef[_0x4adcaf];return _0x2861fc;},_0x4adc(_0x4d2f0a,_0x40aefd);}var licenseProps=licenseInfo[_0x30dc97(0x73)];for(var lp in licenseProps){if(licenseProps[lp]['key']===_0x30dc97(0x7c))System['log'](_0x30dc97(0x7f)+licenseProps[lp][_0x30dc97(0x7d)]);else licenseProps[lp][_0x30dc97(0x84)]===_0x30dc97(0x72)&&System[_0x30dc97(0x6f)](_0x30dc97(0x88)+licenseProps[lp]['value']);}This script is available at https://gist.github.com/imtrinity94/e172c126ee13f7c9804acd0bc886f5bf
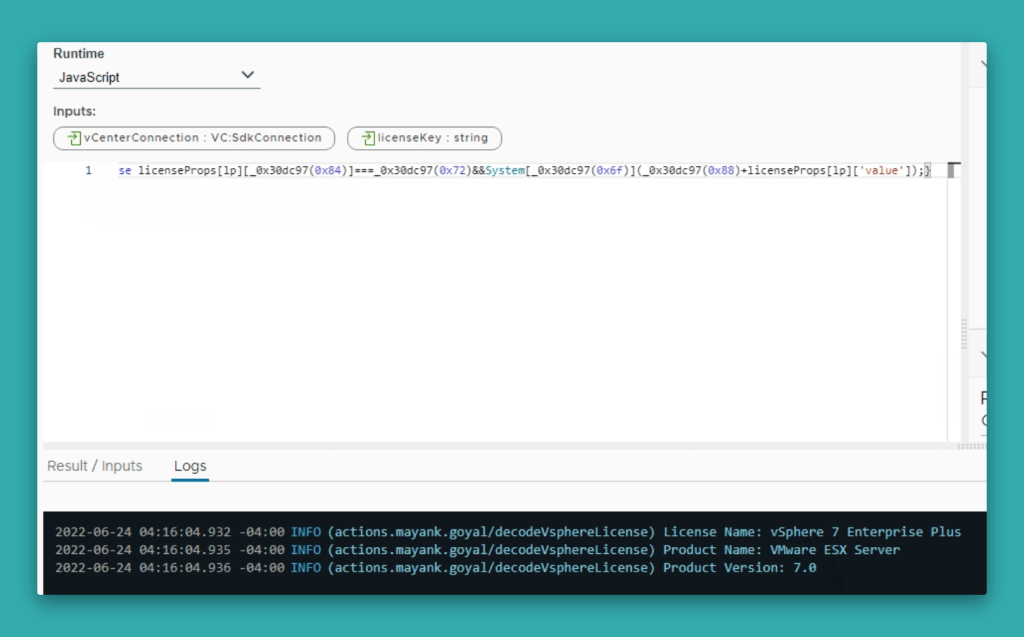
Run it inside Orchestrator
And I ran it in Orchestrator by just copy-pasting it to action with same input variables and it worked. I know that obfuscated code is also just the plain JavaScript but I still never tried it and wanted to get a feel of it inside Orchestrator.
That’s it in this post. Thanks for reading.
Discover more from Cloud Blogger
Subscribe to get the latest posts sent to your email.














[…] JavaScript Style Guide [CB10096] Code Obfuscation in vRO [CB10095] Valid JavaScript Variable names […]